On Monday I got to meet Jamie Lewis face-to-face for the first time, and we had a great talk about a lot of things. We're both looking forward to the upcoming Digital Identity Conference . Chatting about PingID and XNS, Jamie quipped that for longtime industry watchers like us, it becomes necessary to qualify acronyms with date ranges. So for example: XNS 2000 versus XNS 1975 .
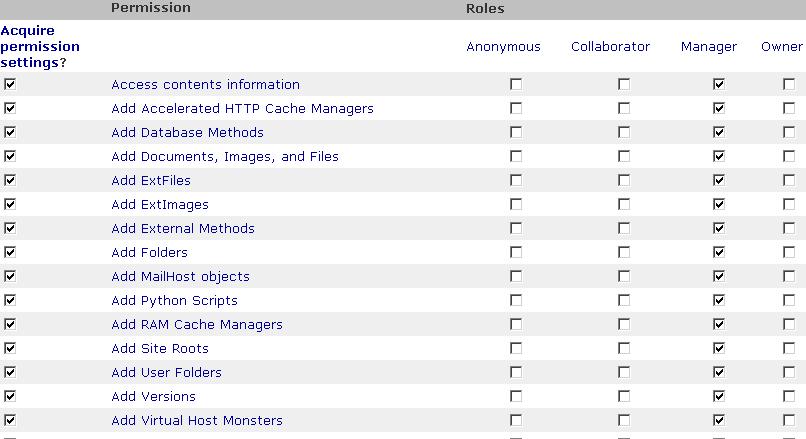
On the subject of security, I aired my concern (shared by acquaintances at Baltimore Technologies ) that ACLs don't scale. Even if we can layer a permissions matrix on top of web services, the combinatorial explosion of that matrix will create complexity that nobody can understand or manage. The example here is from Zope, but we've all done this -- and it's unthinkable to do it for thousands or millions of rows and columns.
Jamie agreed, and cited a speech by Dan Geer, who's CTO of @stake , in which Geer advanced the notion that ACLs don't scale, but surveillance and accountability do. Here's an excerpt from the full text of the speech Geer made to the Security Industries Middleware Council ( SIMC ):
If the access control matrix eventually scales out of reach, what then? I submit that where the geometric scaling of access control will kill it in the end, accountability stands ready. This is not to say that I like pervasive, universal accountability, per se, but the only reason a free society works is that you can pretty much do anything though if you screw up badly we will find you and make you pay. Accountability is like that, i.e., it is a log processing problem. When it comes to processing logs, Moore's Law is on your side. Observability is on your side as it puts off the deductive costs to later when you need to invest in making them, and you can probably use grid computing as a log processing tool since the web search engines have got that pretty well worked out. Because disk prices fall faster than CPU prices and because network prices fall faster still, log information storage and availability are just not problems.
I'll buy that. As Jamie points out, this mirrors how things work in the real world. No ID and access-control mechanism can prevent me from committing a crime. But an eyewitness or a surveillance camera can hold me accountable.
Former URL: http://weblog.infoworld.com/udell/2002/08/28.html#a389